The dangerous Android banking trojan that we first informed about in the beginning of this year has found its way to Google Play again, now stealthier than ever.
Dubbed BankBot, the banking trojan has been evolving throughout the year, resurfacing in different versions both on and outside Google Play. The variant we discovered on Google Play on September 4, is the first one to successfully combine the recent steps of BankBot’s evolution: improved code obfuscation, a sophisticated payload dropping functionality, and a cunning infection mechanism abusing Android’s Accessibility Service.
Misuse of Android Accessibility has been previously observed in a number of different trojans, mostly outside Google Play. Recent analyses from SfyLabs and Zscaler have confirmed that the crooks spreading BankBot managed to upload an app with the Accessibility-abusing functionality to Google Play, only without the banking malware payload.
The “complete puzzle” featuring the banking malware payload managed to sneak into Google Play masqueraded as a game named Jewels Star Classic (it is important to note that the attackers misused the name of popular legitimate game series Jewels Star by the developer ITREEGAMER, which is in no way connected to this malicious campaign).
We have notified Google’s security team of the malicious app, installed by up to 5000 users before getting removed from the store.
How does it operate?
When the unsuspecting user downloads Jewels Star Classic by the developer GameDevTony (Fig. 1), they get a functioning Android game, only with some hidden extras – banking malware payload lurking inside the game’s resources, and a malicious service waiting to be triggered after a pre-set delay.
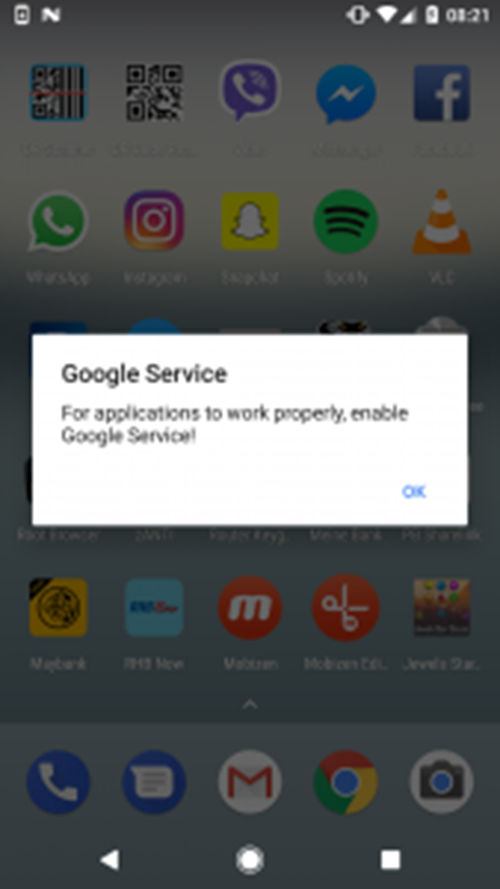
The malicious service is triggered after 20 minutes from the first execution of Jewels Star Classic. The infected device shows an alert prompting the user to enable something named “Google Service” (note: the malicious alert appears independent of the user’s current activity, and with no apparent connection to the game).
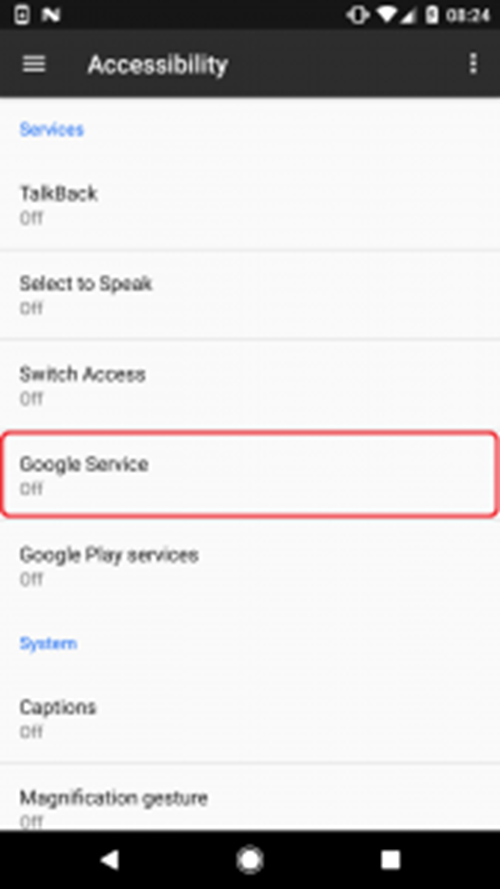
After clicking on OK, which is the only way to stop the alert from appearing, the user is taken to the Android Accessibility menu, where services with accessibility functions are managed. Among legitimate ones, a new service named “Google Service” is listed, created by the malware. Clicking on it displays a description taken from Google’s original Terms of Service.
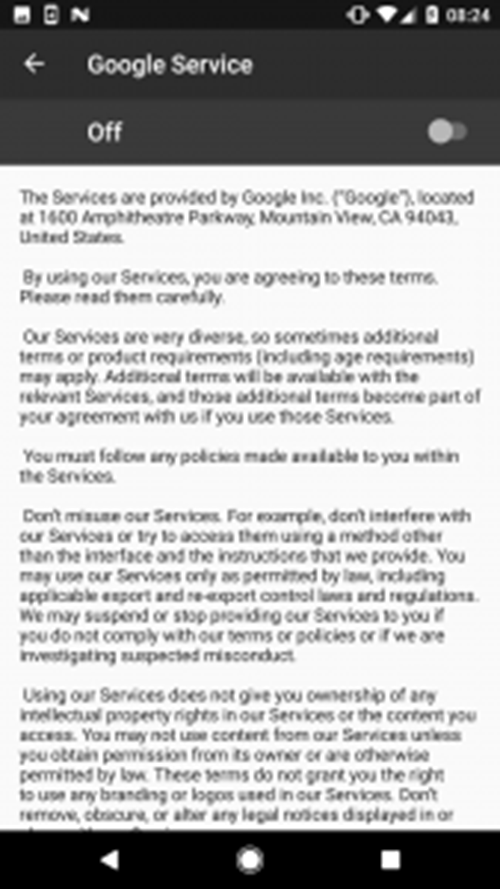
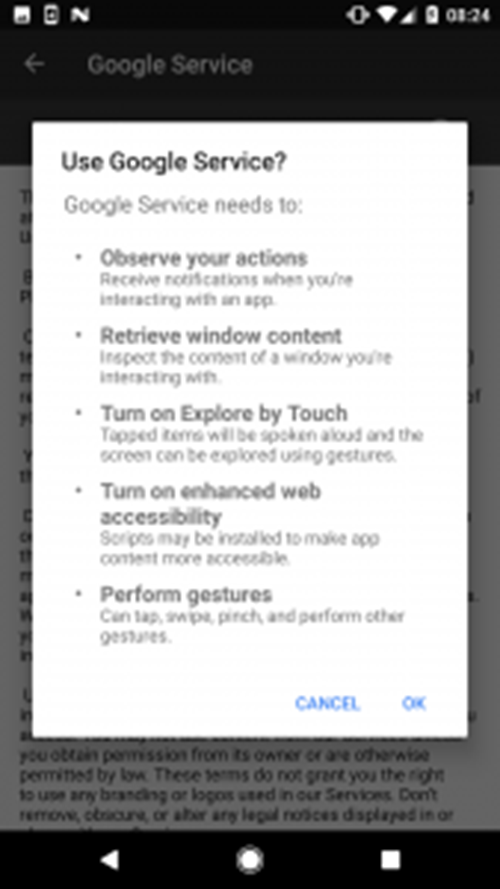
When the user decides to activate the service, they see a list of required permissions: Observe your actions, Retrieve window content, Turn on Explore by Touch, Turn on enhanced web accessibility and Perform gestures (Fig. 5).
Clicking on OK grants accessibility permissions to the malware’s own accessibility service. By granting these permissions, the user gives the malware a free hand – almost literally – to carry out any tasks it needs to continue its malicious activity.
In practice, after accepting the permissions, the user is briefly denied access to their screen due to “Google service update” – needless to say, not initiated by Google – running in the foreground (Fig. 6).

The malware uses this screen to cover its next steps – clicking on user’s behalf using the previously obtained accessibility permissions. While the user waits for the fictitious update to load, the malware carries out the following tasks:
- allow installing apps from unknown sources
- install BankBot from assets and launch it
- activate device administrator for BankBot
- set BankBot as default SMS messaging app
- obtain permission to draw over other apps
After these tasks are successfully carried out, the malware can start working towards its next goal: stealing the victim’s credit card details. As opposed to other BankBot variants that target an extensive list of specific banking applications and impersonate their login forms in order to harvest entered credentials, this one focuses exclusively on Google Play – an app every Android user has preinstalled on their device.
When the user launches the Google Play app, BankBot steps in and overlays the legitimate app with a fake form requesting user’s credit card details.(Fig. 7).
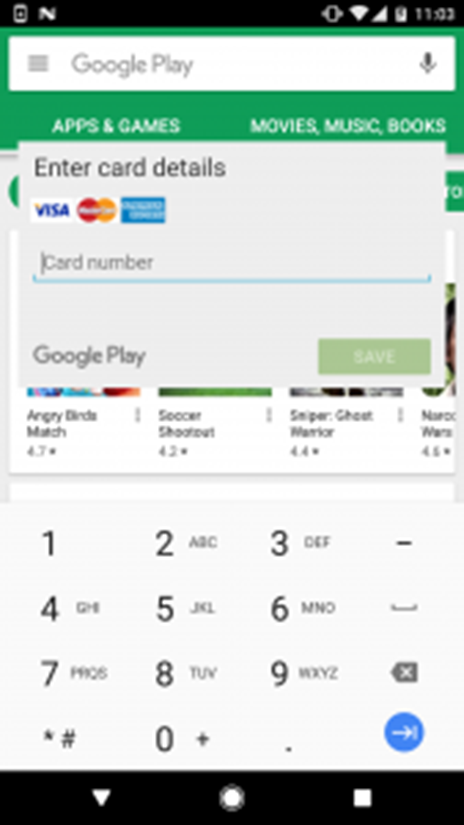
If the user falls for the fake form and enters their credit card details, the attackers have essentially won. Thanks to BankBot setting itself as the default messaging app, it can intercept all SMS communication going through the infected device. This enables the attackers to bypass SMS-based two-factor authentication on the victim’s bank account – the last potential obstacle between them and the victim’s money.
What makes it so dangerous?
In this campaign, the crooks have put together a set of techniques with rising popularity among Android malware authors – abusing Android Accessibility Service, impersonating Google, and setting a timer delaying the onset of malicious activity to evade Google’s security measures.
The techniques combined make it very difficult for the victim to recognize the threat in time. Because the malware impersonates Google and waits for 20 minutes before displaying the first alert, the victim has very little chance to connect its activity to the Jewel Star Classic app they’ve recently downloaded. On top of that, the many different names the malware uses throughout the infection process significantly complicate efforts to locate and manually remove it.
How to clean infected device?
If you’re downloading many different apps from Google Play and elsewhere, you might want to check if you haven’t reached for this malware.
Checking your device for Jewels Star Classic is not enough, as the attackers frequently change up the apps misused for BankBot’s distribution. To see if your device has been infected, we recommend you go after the following indicators:
- Presence of an app named “Google Update” (shown in Fig. 8 and found under Settings > Application manager/Apps > Google Update)
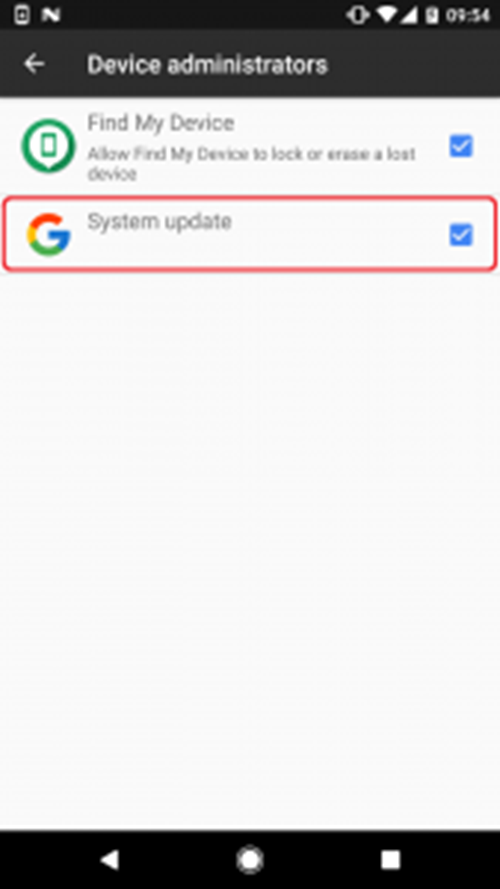
- Active device administrator named “System update” (shown in Fig. 9 and found under Settings > Security > Device administrators).
- Repeated appearance of the “Google Service” alert (shown in Fig.2)

If you find any of the mentioned indicators, your device may well have been infected with this BankBot variant.
To manually clean your device, you would first need to disable device administrator rights for “System update”, then proceed to uninstalling both “Google Update” and the associated trojanized app.
However, finding which trojanized app started the infection (like, in this case, Jewels Star Classic) is tricky due to the 20 minute delay of malicious activity, as well as the fact that the app works as expected. To detect and remove the threat with all its components, we recommend using a reliable mobile security solution.
ESET security products detect and block this variant of BankBot as Android/Spy.Banker.LA.
How to stay safe?
Besides using a reliable mobile security solution, there are other things you can do to avoid falling victim to mobile malware:
- Whenever possible, favor official app stores over alternative ones. Although not flawless, Google Play does employ advanced security mechanisms, which doesn’t have to be the case with alternative stores.
- When in doubt about installing an app, check its popularity by number of installs, ratings and content of reviews.
- After running anything you’ve installed on your mobile device, pay attention to what permissions and rights it requests. If an app asks for intrusive permissions – even more so if Accessibility-related – read them with caution and only grant them if absolutely sure of the app’s reliability.
Read More: Are we still vulnerable to malware in 2017?
What is BankBot?
First detected by ESET on December 26, and first analyzed by Dr. Web, BankBot is a remotely controlled Android banking trojan capable of harvesting banking details using phony login forms for a number of apps, intercepting text messages in order to bypass 2-factor-authentication, and displaying unsolicited push notifications.
Shortly after the discovery of the apps trojanized with BankBot on Google Play in the beginning of 2017, we have confirmed the malicious apps were derived from source code made public on underground forums in December 2016. The public availability of the code has led to a surge in both the number and sophistication of mobile banking trojans.
