Lack of cybersecurity skills causing slow adoption of cloud services: Report
40% of cloud services are commissioned without the involvement of IT, leading to more security risk for companies, states, global computer security software company, Intel Security’s cloud security report – ‘Building Trust in a Cloudy Sky’. Between September to December last year, Intel Security claims to have surveyed over 2,000 IT professionals and senior technical decision makers from small, medium and large sized organizations from 12 countries for this report, and revealed that trust now outnumbers distrust for public clouds by more than 2-to-1.
David Allott, Director, Cyber Defense, APAC, Intel Security stated that many organizations in Southeast Asia have incorporated a ‘Cloud First’ strategy into their architectures.
 According to the report, about 85% of those surveyed store some or all of their sensitive data in the public cloud. Personal customer information is the most likely type of data to be stored in public clouds, kept there by 62% of those surveyed. The report states that most organizations view cloud services as or more secure than private clouds, and more likely to deliver lower costs of ownership and overall data visibility. 29% stated to distrust public cloud completely which, according to the company, has gone down from 50% in 2015.
The report claims that the rationale for companies to store personal customer information on the public cloud appears to be influenced by online business models. Industries with a high proportion of online transactions are the most likely to store their customer data in the public cloud, such as utilities (79%), services (73%), insurance (65%), and finance (64%). Government organizations were more likely to keep staff information (66%) than customer information (59%) in the cloud.
According to the report, about 85% of those surveyed store some or all of their sensitive data in the public cloud. Personal customer information is the most likely type of data to be stored in public clouds, kept there by 62% of those surveyed. The report states that most organizations view cloud services as or more secure than private clouds, and more likely to deliver lower costs of ownership and overall data visibility. 29% stated to distrust public cloud completely which, according to the company, has gone down from 50% in 2015.
The report claims that the rationale for companies to store personal customer information on the public cloud appears to be influenced by online business models. Industries with a high proportion of online transactions are the most likely to store their customer data in the public cloud, such as utilities (79%), services (73%), insurance (65%), and finance (64%). Government organizations were more likely to keep staff information (66%) than customer information (59%) in the cloud.
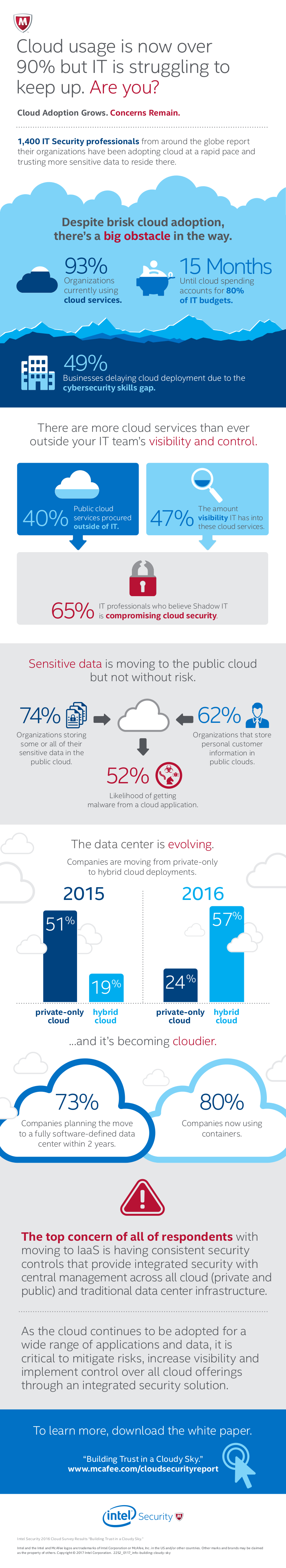
“Those who have yet to do so, are rapidly striving towards cloud adoption. We saw that in 2016, 57% of organizations shifted to hybrid cloud models, compared to just 24% in 2015. This is an indication of the ever growing state of cloud adoption among organizations.”
Trusting the cloud
 According to the report, about 85% of those surveyed store some or all of their sensitive data in the public cloud. Personal customer information is the most likely type of data to be stored in public clouds, kept there by 62% of those surveyed. The report states that most organizations view cloud services as or more secure than private clouds, and more likely to deliver lower costs of ownership and overall data visibility. 29% stated to distrust public cloud completely which, according to the company, has gone down from 50% in 2015.
The report claims that the rationale for companies to store personal customer information on the public cloud appears to be influenced by online business models. Industries with a high proportion of online transactions are the most likely to store their customer data in the public cloud, such as utilities (79%), services (73%), insurance (65%), and finance (64%). Government organizations were more likely to keep staff information (66%) than customer information (59%) in the cloud.
According to the report, about 85% of those surveyed store some or all of their sensitive data in the public cloud. Personal customer information is the most likely type of data to be stored in public clouds, kept there by 62% of those surveyed. The report states that most organizations view cloud services as or more secure than private clouds, and more likely to deliver lower costs of ownership and overall data visibility. 29% stated to distrust public cloud completely which, according to the company, has gone down from 50% in 2015.
The report claims that the rationale for companies to store personal customer information on the public cloud appears to be influenced by online business models. Industries with a high proportion of online transactions are the most likely to store their customer data in the public cloud, such as utilities (79%), services (73%), insurance (65%), and finance (64%). Government organizations were more likely to keep staff information (66%) than customer information (59%) in the cloud.
Cybersecurity skill shortage
The survey revealed that there is an ongoing shortage of security skills which is affecting cloud deployment. 49% of the organizations reported the lack of cybersecurity skills leading to the slowed adoption or usage of cloud services, possibly contributing to the increase in Shadow IT activities. Hence, 65% think Shadow IT is interfering with keeping the cloud safe and secure. Another 36% report they are experiencing a scarcity but are continuing with their cloud activities regardless. Only 15% of those surveyed state they do not have a skills shortage.Unchecked cloud services
Because the cloud services can be procured easily, 40% stated that these services are now commissioned without the involvement of IT. 52% state that they have tracked malware incidents to a SaaS application. SaaS applications have added a new threat vector for malware to enter networks and systems. As a result, 65% of IT professionals think this phenomenon is interfering with their ability to keep the cloud safe and secure. According to the report, SaaS users were most concerned about protecting sensitive data moving to and from the cloud, understandable given that half have experienced a malware infection from SaaS applications and a quarter have suffered a data breach. The second most common concern of SaaS users was cost, reinforcing how mature these services are becoming.Data Center concerns
Intel Security states that the number of organizations using private cloud has dropped to 24% in 2016 from 51% in 2015 and hybrid cloud usage has increased from 19% to 57%. Organizations are needed to evolve to a highly visualized, cloud-based infrastructure for moving to hybrid private/public cloud architecture. The report states that 52% of an organization’s data center servers are virtualized, 80% are using containers — 36% using containers inside IT, 18% outside IT, and 29% both inside and outside the IT department — and most expect to have the conversion to a fully software-defined data center completed within two years.Conclusion
- The report states that cloud is here to stay as businesses trusting them with a wide range of applications and data, much of it sensitive or business critical. As cloud is effective and efficient, there needs to be security in advance to detect threat.
- Security concerns about clouds are maturing, moving from vague and generic fears about breaches to more detailed issues about protecting data at rest and in transit, consistently configuring and enforcing security policies, and controlling identity and access. Unfortunately, the scarcity of security skills is also real, and is an issue for most organizations, regardless of industry, country, or size.
- Increased use of public cloud services may help alleviate the impact of the security skills shortage, as organizations leverage the broad and deep security talent pools that are present in most major cloud providers.
What the survey recommends
- Attackers will look for the easiest targets, regardless of whether they are public, private or hybrid. Integrated or unified security solutions that provide visibility across all of the organization’s services could be the best defense.
- User credentials, especially for administrators, will be the most likely form of attack. Organizations need to ensure they are using authentication best practices, such as distinct passwords, multi-factor authentication and even biometrics where available.
- Security technologies such as data loss prevention, encryption and cloud access security brokers (CASBs) remain underutilized. Integrating these tools with an existing security system increases visibility, enables discovery of shadow services, and provides options for automatic protection of sensitive data at rest and in motion throughout any type of environment.
- Organizations need to evolve toward a risk management and mitigation approach to information security. They should consider adopting a Cloud First strategy to encourage adoption of cloud services to reduce costs and increase flexibility, and put security operations in a proactive position instead of a reactive one.
